How To Install Winword Exercise
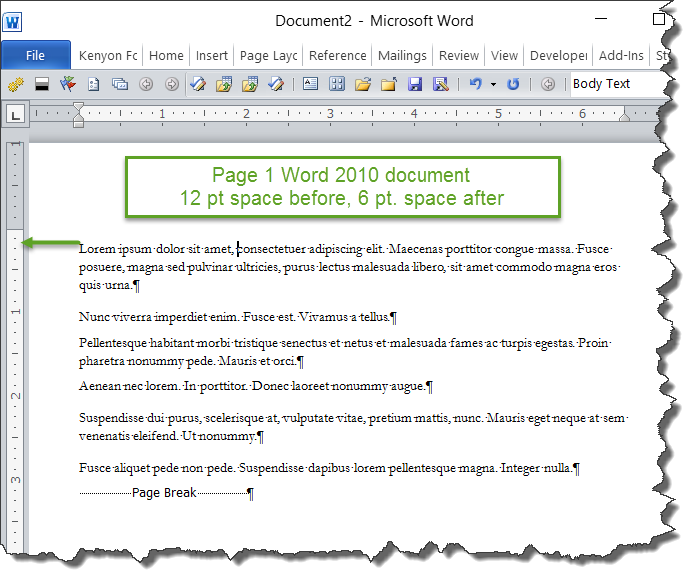
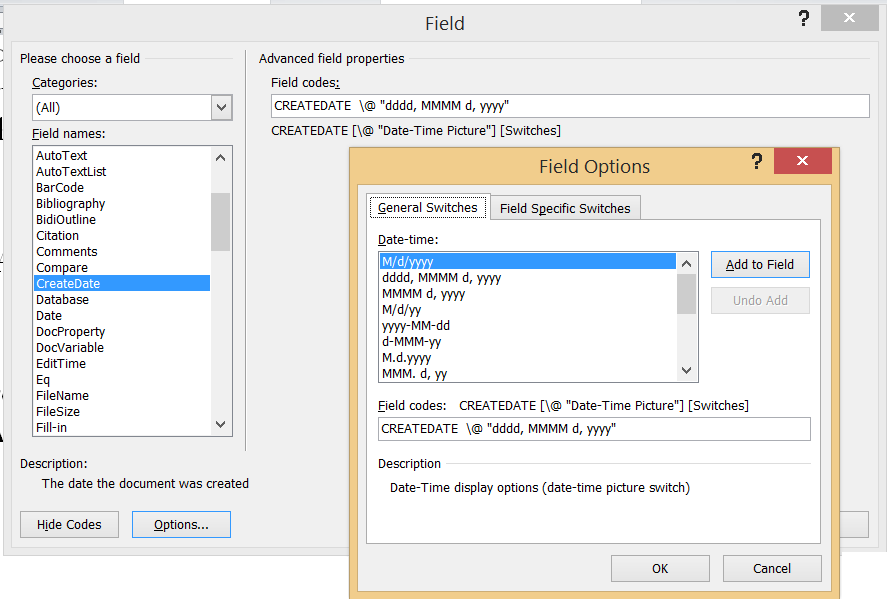
On the Page Layout tab, in the Page Setup group, click the Breaks button and then, in the list, click Page. The first time we instruct you to click a specific button in each exercise, we display an image of the button in the page margin to the left of the exercise step. If differences between your display settings and ours cause a.
Hi Everyone, I know you're all fed up with 'Happy New Year' but I will offer such wishes anyway! In 2014 protecting your information will (should) be at the top of your list.
Unlike the 3 or so weeks of drinking 64 oz of water and exercising daily for 30 minutes, this is one promise that we're all expected to be better about. With this in mind, the next few posts will be dedicated to 'tracking' your important documents. One often ignored aspect of RMS is the ability to mine (quite impressive) logs for hits of things not being 'quite right'. Said differently, even the practice of using RMS on 'somewhat sensitive' documents with a 'Your Company — All employees' will yield a goldmine of very impressive usage data.
At Microsoft we often send out 'vision' documents, memos, etc with RMS protection so that we (the document owners, area leaders) can get a sense of the readership. Driver Pack Solution 2013 Indir Tek Link. Logs don't lie. Today's post was co-authored with Amrita, our logging expert.
Reminders: Follow us on twitter () and join in our our new RMS peer community. Cheers, Dan (on behalf of our wonderful team) PS: Though this post is focused on Azure RMS, the AD RMS offering has wonderful SQL logs too so similar sentiments apply especially the next post on how to use the new Microsoft 'Power BI' to produce fantastic reports.
————————————- Hi, Amrita here, Let's talk logging! Using the usage logging feature in Microsoft Rights Management Service (Azure RMS), with a few simple steps you can capture and view logs for every administration action and request for your protected content to Microsoft Rights Management as soon as it happens.
This information is useful for a variety of reasons: • Analyzing data access for business insight. Using these logs, you can create reports and drive insights such as: who is accessing your sensitive data, what devices are being used for access, which locations are your users accessing data from, and report on which users have read a given document. • Monitoring for abuse.
You can access your logs in near-real-time (delay: Import-Module AADRM PS C:Windowssystem32>Connect-AadrmService -verbose 3. When prompted for credentials, enter your Azure RMS tenant credentials (these credentials should have Global Administrator privilege) and wait to be authenticated.
Example: Username: Password: **************** 4. Run the following commands to specify the Azure RMS where you want your logs. How To Install Fedora 8 On Windows 7 on this page. Replace the example access key in the ConvertTo-SecureString cmdlet with the storage access key that you copied from the Windows Azure management portal in step #2->#5 above. Replace the example storage account “RMSBILogs” with your real storage account name. PS C:Windowssystem32>$accesskey = ConvertTo-SecureString'wUjKVV14XXUCrdpuLsIa8yQ5IgUmLSOLmlgS/CcHNZXiurEORjTItdtPf4OpCaIwGNyijjMPxvDEOG21HRKR7A==' –asplaintext -force PS C:WindowsSystem32>Set-AadrmUsageLogStorageAccount -StorageAccount RMSBILogs -AccessKey $accesskey RMSBILogs was set as the storage account for the usage log feature for the Rights management service. PS C:Windowssystem32.
New News
- Mard Maratha Dj Song Free Download
- Flytampa Boston V3 Fsx Aircraft
- Intelligent Investor Ebook Mobi
- Chatology Download Chrome
- Pc Optimizer Pro Serial Keygen Download Cs6
- Farmacognosia Da Planta Ao Medicamento Pdf Download
- Autodesk Inventor 2013 X64 Keygen
- Wurth Wow Keygen Скачать
- Hima Elop Ii Crack
- How To Download All Your Hotmail Emails Not Being Delivered
- Mind Cracking Riddles
- Hp Compaq Dc7900 Small Form Factor Pc Drivers Download
- Free Download Ccm Bicycle Speedometer Manual Programs
- Pocket Monsters Green Beta Download
- Driver Scheda Video Hp Proliant Ml110 G3